Telco Products
NetMaut Policy Platform
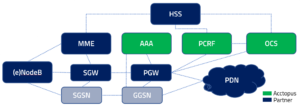
The NetMaut platform is an extensive policy management system that controls the access of mobile customers into the data network.
As an enabler in the service layer of mobile network infrastructure, NetMaut has interfaces to the relevant databases and CRM systems of the mobile operators.
Your individual tariff portfolio is exactly mapped in the NetMaut system. Through a sophisticated set of rules, NetMaut determines who may access the internet and other service offerings in which quality of service. To control a session NetMaut considers, for example, the tariff settings, the location, and the device of a customer.
Options for 2G, 3G, 4G and WiFi
NetMaut was initiated in the GPRS and early UMTS area. It started with a RADIUS server and RADIUS-based policy and charging control and evolved to a full-featured 4G Platform with the required Diameter protocols and connecting to HSS or User repositories.
NetMaut Modules
The NetMaut platform includes the following modules:
- NetMaut Tariff Designer – modular design of an almost unlimited number of tariffs
- NetMaut PCRF – policy function that decides on session configuration and QoS
- NetMaut RADIUS Server – subscriber authentication and authorization
- NetMaut OCS (Online Charging System) – quota management
- NetMaut SPR (Subscriber Profile Repository) – subscription management
Are you interested in our Network Access and Policy Solution?
NetMaut Tariff Designer
The NetMaut Tariff Designer allows designing an almost unlimited number of tariffs in a truly modular system. Based on various attributes – such as volume, duration or Quality of Service – numerous tariffs may be configured and later on assigned to the subscribers.
Tariff Flexibility
Each tariff option may have all or a selection of the following attributes:
- available data volume
- maximum speed (upload/download)
- validity in the period from/to (e.g. day, week, month)
- validity in the time from/to (e.g. at the weekend from 9.00 am – 5:00 pm)
- validity at specific locations (assignment to footprints)
- actions carried out after usage of available data volume
(like limiting the bandwidth or redirecting to a booking platform) - actions carried out at specified thresholds (like sending an SMS “n % volume used up”)
- immediate activation or activation on first use
- allocation of user groups (several users share quota)
The assignment of tariffs to subscribers can vary from provider to provider. The tariffs may for example be stored as Service Option Codes for the subscriber in the CRM or they are booked online by the customer and provided to the NetMaut SPR by the booking platforms.
Tariff Calculation
NetMaut uses a comprehensive calculation logic to determine the available data volume and the QoS values provided for a subscriber. This logic cumulates and prioritizes the tariff attributes according to policies agreed upon with the provider.
Here is an example:
- If a customer has several data volume options, the volumes of these options add up.
- If these options have different bandwidth settings the QoS can be adapted to the settings of the unused options.
- If the customer books up a new option which only consists of a bandwidth option the QoS for the volume of the other options is raised accordingly.
- If the customer changes the location the QoS may be adapted. This allows the creation of roaming offers, which use the full bandwidth in the national context and the national volume with a limited bandwidth abroad.
Supported Tariff Models
The NetMaut calculation logic includes various tariff models which differ with regard to the methods used for calculating volume and determining QoS attributes.
StandardFlex
The name is a pure understatement since this method allows the fastest time-to-market for new products.
In the StandardFlex model, each combination of tariff options has fixed volume and QoS attributes. If a combination changes (an option is added or dropped) the attributes for the customer are completely re-calculated.
The preset attributes can be different for different locations (footprints).
CombiFlex
In the CombiFlex model volume and time quotas from all Service Option Codes booked by a subscriber are added up. Respectively, the best value for each attribute is determined by a set of rules.
This allows customers the flexible booking and canceling of tariff attributes in a modular way and thus almost unlimited combinations of tariffs.
PremiumFlex
In the PremiumFlex model, the validities for the use of a booked tariff option (duration and period of time) are managed in the NetMaut system.
The CRM of the mobile service provider or a mediation platform could for example create an option, which is valid “from now until next Sunday 11:59:59 pm”.
GroupFlex
The GroupFlex model summarizes the tariff attributes for groups of users. This allows creating tariffs for families or teams in which all group members may book options into a pool and use it collectively.
On each usage and booking, NetMaut adapts volume and QoS dynamically and optionally informs all group members about thresholds and booking options.
Most features of the tariff models can be combined per subscriber and footprint ensuring the highest flexibility. We support you in figuring out which models best fit your current and your future needs.
Enterprise Customers and Reseller
In addition to these models we also provide customized configurations which allow mobile service providers to develop separate tariffs and flows for enterprise customers or resellers like for example:
- special configurations for specific access points (APN)
- VPN configurations for customer groups
- multi-APN failover configurations
NetMaut 4G PCRF
The NetMaut PCRF (Policy and Charging Rules Function) is the brain of a mobile data network. It determines which quality of service is granted for data connections.
Based on a number of input parameters from the PGW and on data stored in the SPR the PCRF takes policy decisions in real-time and grants the best values for the current session at the current point in time.
The PCRF controls network elements which are usually decentralized such as Packet Gateways, Traffic Optimizer systems, or TDF (Traffic Detection Function), also known as DPI systems (Deep Packet Detection).
By setting triggers the PCRF moreover requests information in case of status changes in order to verify, and if required modify, its latest decision based on the new information.
Input Parameters (Examples)
The PCRF accepts various different input parameters transmitted for example by the Diameter Gx messages of the Packet Gateway. The following list shows the most frequently used information:
- subscriber ID (MSISDN or IMSI)
- IP address of the device
- type of IP-CAN (GPRS, LTE, etc.)
- IP-CAN bearer modus
- IP-CAN bearer parameter
- request type (initial, modification, etc.)
- location of the subscriber
- PDN ID
- PLMN identifier
- …
Supported Interfaces
The NetMaut PCRF supports a number of interfaces and applications:
(growing as demand araises)
- Diameter Gx – interface from PCEF
- Diameter Sy – interface to OCS
- Diameter Sp – interface to SPR
- UD (SOAP) – interface to the provisioning
- UDR (LDAP) – interface to user information held by the provider
and for integrations beyond the standard
- HTTP (REST, SOAP)
- LDAP
- …
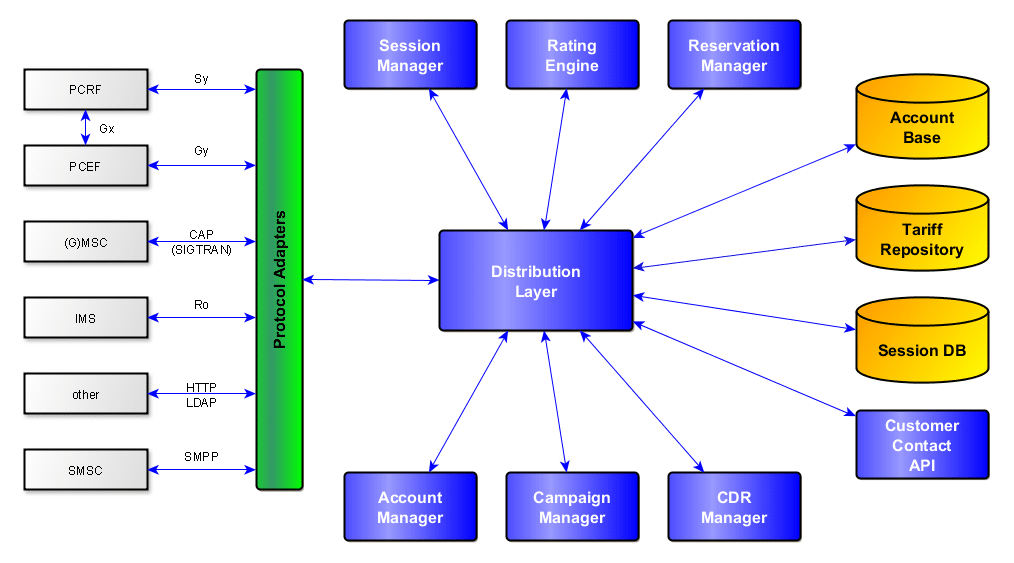
NetMaut 4G OCS
Acctopus NetMaut OCS (Online Charging System) manages available quota in terms of data volume, time, or units (e.g. number of smses). It serves the OCS requirements for more than 32 million subscribers, having 15 million concurrent sessions in a single environment.
As an OCS, it features the major functionalities of
- an Account Manager
- a Session Manager
- a Balance Manager
- a Charging Manager
- a Campaign Manager
- a Reservation Manager
as well as a flexible Rating Engine to calculate the tariff options booked by the subscriber.
Functionalities of NetMaut OCS
Account Manager
The Account Manager maintains the structure of dynamic subscription data with monetary equivalence.
An account can have one or more users associated with it and may have balances/counters of currency or a unit type.
The Account Manager keeps a configurable transaction history in the OCS account data structure.
In principle, the Account Manager
- checks the account balance,
- supports account balance updates (credit/debit),
- supports account balance reservations,
- gets/sets counters to the Admin GUI and the API and
- gets/sets the expiry date of the (pre-paid) account.
Session Manager
The Session Manager maintains the chargeable or free of charge sessions.
In most cases, a session is a data communication and might be of type data session (e.g. 4G or GSM) or of type duration e.g. of a movie, streamed to the end-user. A session also might be a voice call, if not counted as a data session.
Sessions always carry parameters to identify (at least) the user, the device, the location, the communication originator, the consumer, and many more, depending on the type of session.
During and after the session these parameters are used for rating, charging, and for CDR creation.
The Session Manager keeps a history of the sessions for troubleshooting and reporting for a configurable period of time.
Charging Manager
The Charging Manager provides real-time charging and authorization of resource usage. It supports session based charging as well as event based charging, both immediate and with unit reservation, where the reservation task is maintained by the Reservation Manager.
To support these tasks, the Charging Manager collects information related to a chargeable event, which has been formatted, transferred and evaluated in order to make it possible to determine the usage the subscribers account balance may be debited (online charging) or for which the charged party may be billed (offline charging).
Every chargeable event is evaluated for type of service, location of usage, time of day and checked against the subscriptions, the user has on her account or against products, the user has to be charged for as single charge or as start of a recurring charge. To do so, the Charging Manager gets its information from the Rating Engine.
Campaign Manager
The Campaign Manager helps to kick off marketing campaigns for a certain group of subscribers. It is the most efficient way to start special discounts or free of charge units for volume or time units or for setting up a higher QoS for a certain period of time, if supported by the PCRF or if accompanied with NetMaut PCRF.
Campaigns might be set up within minutes, without involving the configuration of several other systems. The operator can manage all types of large-scale, multi-wave, and cross-channel campaigns, execute and measure them.
Balance Manager
The Balance Manager cooperates with the Account Manager, but takes care of the subscriber account balances (subscriptions), instead of the subscriber and users.
Account balances include units/currency or subscriber counters, e.g. SMS/MMS/volume/time used per time unit (day/week/month/year).
Reservation Manager
The Reservation Manager gets involved during sessions or at events, which require a unit reservation.
Unit reservation is the standard way to prevent fraud scenarios, where e.g. a prepaid subscriber places a phone call after her monetary units are depleted.
Interfaces and Protocols
The OCS includes the interfaces required for the full MVNO integration and supports voice, data, and SMS charging.
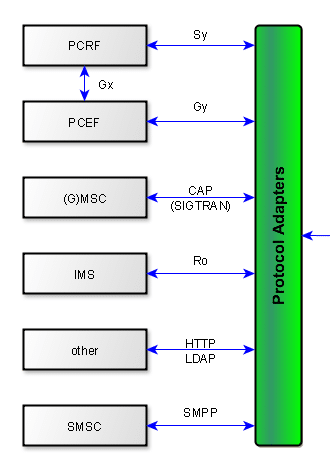
The Diameter Gy interface sits between the PCEF (e.g. on a PGW) and the OCS. It is used for online charging of data sessions. Diameter Gy is a subset of the Ro interface.
The Diameter Ro interface sits between the AS and the OCS for charging of IMS & LTE sessions.
The Diameter Sy interface sits between the OCS and the PCRF. Via this interface, the PCRF might subscribe policy counter values from the OCS, related to subscribers who have active data sessions at a PGW which is controlled by the PCRF, using Diameter Gx.
All Diameter applications might either have their peer on the far end entity or might be connected to a DRA in between the far end entity and the NetMaut OCS.
CAP, the CAMEL Application Part protocol, is used when the subscriber is roaming between networks, allowing the home network to monitor and control calls made by the subscriber. CAMEL provides services such as prepaid roaming services and authenticates the services in accordance with the account balance of the subscriber’s account settings, which might come from an available unit or available free of charge.
NetMaut OCS has a powerful function that lets MVNO’s services platform interrogate or book services even using HTTP/ LDAP, which are not primarily designed or foreseen for this application, but help to speed up the evolution of product design at the MVNO.
Short Message Peer-to-Peer (SMPP) is used to send status information to the subscriber (e.g. balance notifications) as well as to receive balance upgrades, sent by the subscriber to the MVNO’s charging system, which takes these upgrades and – if successfully applied – creates CDRs to the billing system.
For charging of SMS, the SMSC might support Diameter Ro or can be interfaced using HTTP/ SOAP.
Integration of the NetMaut OCS
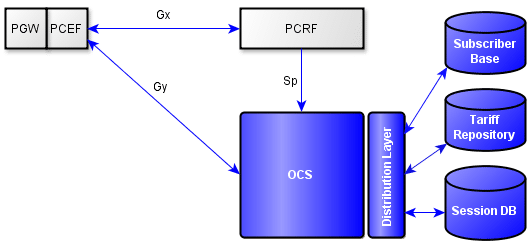
The OCS controls the data usage of the subscribers through the internal “Flow-Based Service Data Credit Control Function” to the PCEF (Policy Charging and Enforcement Function) in the gateway (GGSN/PGW).
During the session, the OCS uses Diameter Reauthentication Requests (RAR) to control the volume and time quotas.
The quotas that are managed by the OCS are sent to the gateway in parts or completely for internal management. Each time a volume limit or a preset time has been reached, the gateway sends a status message about the data usage (Credit Control Request) to the OCS. Based on this status the OCS takes its next decisions.
The OCS communicates with the subscriber and session databases to get the relevant information for the calculation of the available quotas.
The PCRF can communicate with the OCS via a Diameter Sy interface to request quota status changes (Spending Limit Reports), in order to change the PCC rules respectively.
NetMaut SPR
The NetMaut SPR (Subscriber Profile Repository) manages subscriber information such as tariff data and booked options.
Integration of the NetMaut SPR
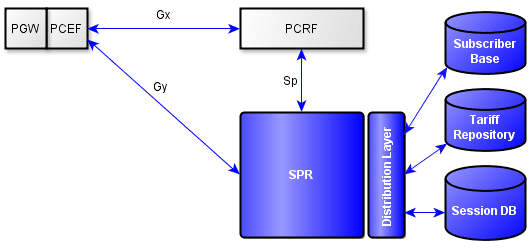
Based on the stored data the SPR extracts the policies and profiles which are provided to the PCRF for the session control.
The NetMaut SPR either is provided with information actively (LDAP write, HTTP REST) or it draws its information from the CRM or the central subscriber databases (LDAP read, HTTP, DNS E.164), as soon as this is initiated by a network trigger.
Stored Data
Essentially the NetMaut SPR contains the following information:
- subscriber categories
- booked/allowed services
- possible QoS characteristics for MBR and GBR
- information relevant for accounting
Supported Interfaces
The NetMaut SPR supports a growing number of interfaces and applications:
- Diameter Sp
- LDAP
- HTTP (REST, SOAP)
- DNS Client (E.164)
NetMaut RADIUS Server
The NetMaut RADIUS Server authenticates and authorizes subscribers accessing a mobile network via gateways (GGSN, PGW), which require the RADIUS protocol for setting up the connection.
The RADIUS Server may be deployed for the following functions:
- authentication and authorization based on user names and passwords (may be relevant in enterprise business)
- allocation of IP addresses
- setting of billing plans and charging identifiers (if the default at the gateway is not sufficient)
- setting of session timeouts
If the RADIUS Server is involved in setting up the session, it can determine how the session is controlled and how the volume and time quota used up during the session are managed.
‘Control’ here refers to configuration of the session (Quality of Service, bandwidths, redirects etc.), while managing the quota is usually referred to as ‘Quota Handling’ or ‘Calculation’.
Integration of the NetMaut RADIUS Server
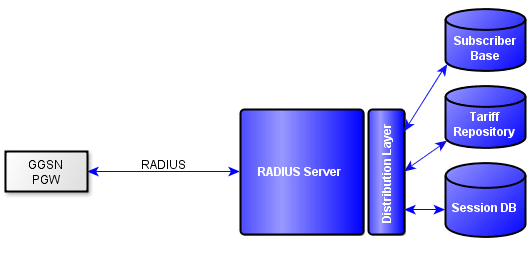
The NetMaut RADIUS Server uses the RADIUS protocol for communication with the gateways (GGSN, PGW).
Session control takes place via
- manufacturer specific QoS attributes
- RADIUS filter lists
- gateway ACLs
- „Change of Authorization“ or „Packet of Disconnect“
Quota management takes place by RADIUS accounting and respective configuration of the accounting intervals.
Why not NASREQ?
In a pure Diameter environment, the RADIUS Server is replaced by a Diameter NASREQ Server. We at Acctopus hold such a Diameter NASREQ Server but we experienced that gateway manufacturer do not keep up this strategy consequently. Moreover, Diameter accounting ended up in a dead-end at the IETF and 3GPP which means that no consistent implementations exist.
Therefore we recommend our customers to use a RADIUS Server until EPC can do without the legacy IP allocation via NASREQ or RADIUS. This will probably take a while considering the fact that gateway interaction in cases of failover is not specified yet and IPv6 networks are not implemented completely so far.